It’s finally happening!! Our 10th DefCamp anniversary starts today and we’re super excited about this special edition!
For those of you who can’t join us this year or missed some presentations, we’ve got you covered with constant updates from the conference.
We’ll do our best to cover as much as possible from the presentations and share with you valuable ideas, useful tidbits and actionable tips from the best infosec speakers.
All you have to do is keep a close eye on the DefCamp blog today and tomorrow and read about the latest news and trends in cybersecurity from #DefCamp 2019.
Day one, 7th November
Arun Mane, Founder, and Director @ Amynasec Labs LLP
Presentation title: Hacking ICS devices for Fun
- ICS stands for the Industrial control system and is critical for every nation, as teach one is connected with every infrastructure.
- ICS Jargons: SCADA (Supervisory control and data acquisition) is a type of ICS / HMI (Human-machine interface) and RTU (Remote terminal units), PLC (programmable logic controller)
- Why the need for ICS Security: ICS is the backbone of each nation’s manufacturing effort and plays a critical role in each nation’s wealth creation, known malware: Stuxnet, Black energy, these ICS systems are also vulnerable.
- Challenges: lack of knowledge, industrial experience needed, hardware setup, cost of hardware
- How to overcome? Try to understand communication protocols, use simulators (Gaspoy, Modbus.py library, Conpot, ScadaBR, ModbusPal
- Useful tools: Nmap, Wireshark, Mbtget, GasPot commands, PLCScan, Metasploit auxiliary/scanner/SCADA
Alex Matrasov, Offensive Security Research Lead @Nvidia
Presentation tile: The Advanced Threats Evolution: Researchers Arm Race
- the average time of vulnerability disclosure in firmware – 6 to 9 months
- the challenge of understanding attack tactics or creating the right mitigation is related to mindset difference between attacker and architect
- SeaBIOS / Coreboot in the cloud
- BMC in many cases expose the different path to update BIOS
- Halvar Flake’s wisdom: “We can’t check the firmware origin”
- Hardware Root of trust
Martin Zember, Red Team @ Zembered Teaming
Presentation title: Why usual pentests suck?
- The talk includes different stories from the Red Team involving a network penetration test, password guessing, email spear-phishing, phone calls, or accessing the building.
- How to get inside a building guarded all time, with cameras, cards, a fence around and other security measures? What engagements to use?
- Getting inside isn’t easy, even though they knew much and had access to the internal network, because the customer wants to know what: an attacker with skills / without IT skills can achieve
- What did they achieve: access to the building, to own cloud.
- Summary: the customer specified the broad scope of the test, and was satisfied with the results.
Inbar Raz, Security Architect & Razier Einhorn, Technical Product Manager @Argus Cyber security
Presentation title: Under Pressure: Real-world damage with TPMS spoofing
- TPMS (Tire pressure monitoring system) – a device that measures the air pressure of a car
- When you deal with one vehicle, you have to receive, analyze and parse, modify and retransmit, which means you have spoofed a TMPS message/signal.
- every single wheel of the car will have a unique ID.
- During the research, they learned that it’s hard to get a good signal, but you need to do the research about the target to understand more and find the signal and extract the documentation needed.
- Collecting multiple packets for statistic analysis to detect patterns and other things, such as TIre ID, CRC parameters.
- Manchester encoding helps to identify when a packet ends and when it is corrupted or not.
- Experimenting with the transmitter setup to see how far you can spoof the signal
- backend setup – > multiple field-deployed Rasperry pie devices
- Challenges: multiple modulations and encoding methods, multiple vendors and packet formats and signal synchronization
- Mitigation to avoid this: make sure you encrypt the transmission, polling-only operation, correlate the signal with other sensors you already have in your car,
- The number one problem is us, the humans: Keep your eyes on the road. Lives depend on it.
- As hackers, we know that where there’s a will, there is a will.
- Failure is part of the learning process. Research is about failing.
- Recommended talk to watch: Ange Albertini – HacK.lu – October 2017

Mircea Hasegan, Software Engineer @Ixia
Presentation title: Consensual Surveillance
- main features for a device (watch) that monitors children: call filter, tracking, the baby monitor
- explaining your kid about the online risks, privacy, and why parents need to monitor their children to avoid the danger they are exposed to
- when you buy the watch, you need to set the initial configuration, which might look like a difficult task to do
- The flow: Once configured, sent data to a server, then you have an application to use, plus a Unique ID associated with the app, and you start seeing the info you are looking for.
- Devices evolve, no matter the type, but the thing is consent. How do you use these devices the right way? It’s sensitive stuff and should be used carefully.
- Children should communicate with their parents and be open about using the device and the implications of the risks.
Jayson E. Street, VP of Infosec @Sphereny
Presentation title: I PWN thee, I PWN thee not!
- We need to get our people to protect the technology
- Customers say: We need a wall to protect from APTs and we’re gonna make the APTs pay for it
- APT= “Adequate Phishing Technique”
- Give employees something to look up to and focus your efforts on educating them
- Employees are not empowered (and educated) to question the unusual < – You have to make sure your employees are aware of this, so educate and empower them!
- Public spaces that are well monitored and highly visible – > “your lobby is not there to be comfortable, but to get people verified”
- it’s not about security, it’s about security fear
- Sometimes we have people monitoring things, but they lack critical thinking.
- What does your SM profile say about you? – Educate employees about what and how to do at Social Media
- Insider threats: sometimes they come from inside the house. Your employees make mistakes because they are not educated properly.
- Phishing is one of the leading causes of compromise but do your employees really take it seriously? -> phishing attacks reach the highest level in three years.
- Do you vet your security systems to make sure they are operating as intended?
- If your company gets breached, DO full disclosure, communicate and quickly respond to this because it matters. Share the information that you got pwned.
- Educated and empowered users, can you ever have enough?
- It’s your responsibility (as a company) to properly educate your users and focus on this.
Chris Kubecka, CEO @Hypasec
Presentation title: The Road to Hell is Paved with Bad Passwords
- With humor and charisma, Chris tells us about ISIS malware attacks and gives us details about how the incident management looks like when an embassy is hacked.
- First incident email account breach -> password used for the Saudi Embassy: 123456 (weak password)
- Diplomatic corps sent warning emails out (about extorsion) using CC, not BBC email.
- Another extorsion attempt -> ambassador’s secretory personal email account was hacked
- Saudi National Threat Day -> hackers asking for $50 million
- Modern problems require modern solutions
- Lessons learned: geopolitics, real human consequences, never trust gifts and be suspicious, always be prepared, and don’t panic in these particular incidents/situations.
- It is imperative that we have freedom of the press.
Koen Vanhees, Security Operations Manager @Cegeka
Presentation title: Machine Learning and Advanced Analytics in Today’s Cyber Security
- Every security pro is a data scientist
- the classic approach for the SOC involving three aspects: technology, people and process
- The future SOC: automation, people and intelligence which implies demand for new skills: scripting skills, taking care of all SOC components instead of following rules, have an open mind for new technologies beyond the comfort zone
- Jupyter notebooks (interactive computing environment)
- what to achieve with automation? Today’s challenge: try to visualize, validate and detection using Machine Learning.
Milan Gabor, CEO @VIRIS
Presentation title: HID (Human Interface Danger)
- Vulnerabilities found in Logitech products referring to the HID devices: keyboard, mouse, game controller, clickers, alphanumerical devices, medical devices, or any other device that meets USB HID specifications
- attack scenarios: USB sticks dropping, classical payload with PowerShell, or classical usage to download and execute malicious files.
- demo: inject into the communication / inject into clickers communication
- demo: pair sniffing
- ideas for HID attacks: USBSamurai – read about it here
- Solutions> Try using Bluetooth devices
Eva Galperin, Director of Cybersecurity EFF
Presentation title: #Spouseware and #Stalkerware: Where Do We Go from Here?
- Most people don’t understand what kind of help they need.
- You can change the system in the way that you’ll help other people
- Stalkerware and spouseware – commercial apps that are used to spy on people’s devices without their consent.
- Example: A mobile spy app for personal catch cheating spouses
- Darkcomet is a RAT developed by Jean Pierre LeSuer
- the difference between #spouseware and #stalkerware is to understand deception (this is the key)
- If you have one of these apps on your device, and you run AV on it, the chances that they are not found are extremely high
- What can AV companies do? Detect them, label it as malicious, stay on top of it, and share samples.
- What can Google do? do a better job policing the Google Play Store
- What can developers do? Have one page/tab where the user can see all of their accounts that have access to their data
- In the US, FTC recently takes action against Retina-X and banned it for making or selling software, until they write better software.
- “I am not a hero or a superhero. You, guys, are!”
- “Look at the systems you wanna change. Find the population you wanna help and go do it!”
Day two, 8th November
Jeff Man, Infosec Curmudgeon Security Weekly
Presentation title: More Tales from the Crypt…Analyst
- Jeff is a highly experienced hacker who worked at NSA and tells amazing stories to the audience.
- It is not enough to be digital, you néed to engage.
- Reminder about Mental health hackers – Don’t forget to live your life. Work-life balance is important.
- In the beginning, it was just the Internet security, not cyber
- Books recommended by Jeff -> Dark territory: The secret history of cyberwar by Fred Kaplan / The cuckoo’s egg by Cliff Stoll (in this one you can learn about the hacking culture)
- one time pad system used for encryption
- Pretty Good Privacy (PGP), the popular mail encryption software program wrote by Phil Zimmerman –
- Primary attack tool used back in times – The Ping Command
- Set user ID is a method used to hack into the systems back then
- reminder: Question everything

Alex J. Balan, Chief Security Researcher @Bitdefender
Presentation tile: Next-Gen IoT Botnets #3 – Moar ownage
- Be mindful of how you read the news, so you can distinguish between real and fake news.
- IoT=Hardware+OS+app+cloud
- IoTs are just websites running on Linux with a significant attack surface on the mobile apps and cloud
- most IOTs have moved to the could because it’s most secure and the botnets will not work anymore there (no ports available so attackers can operate)
- current and upcoming IoTs implementations: not directly accessible to the Internet, more efficient management, decent usage of encryption, or modular architecture. However, not all implementations are that great.
- S3 buckets –
- next hen IoT botnets: buffer overflow in the cloud agent (Kalay platform used for cloud communication), RCE command injection
- Takeaways: IoT is a huge attack surface and is growing insanely fast / Leverage cloud communication to bypass NAT / Vendors need to pentest their product periodically & run bog bounty programs & have proper + unattended update mechanisms.
- RCEs are often found in IoTs and it seems this won’t change anytime soon. More of the security research community needs to focus on this.
- Everything is vulnerable, you just may have not found it yet.
Bia Lewis, CEO@Girls Who Hack
Presentation tile: The U.S. Election System, Can we fix it? YES, WE CAN!
- The 12-year-old girl and the youngest speaker at DefCamp
- The election system has a HUGE attack surface: over 10,000
- More states lack resources and technical expertise, using aging equipment,
- everyone tries to hack the voting system. ALL THE TIME.
- Election officials are not required to report these vulnerabilities
- guidelines are out there, so let’s use them: OWASP, NIST Cybersec framework, OpenSCAP, S.A.F.E Act
- You need to test the reporting system with hackers, using the OWASP top 10 and detect vulnerabilities
- 80% of US voting machines are made by 2 manufacturers: ES&S and Dominion
- the voting machines – all closed source code
- Paper ballots – > there are 2 ways to collect votes: Handmade paper ballot and BMD (Ballot making device)
- Voting machines in the cold storage -> how to secure it? Rember about software updates and apply them
- What is the best voting system? Hand marked paper ballots (counted by hand or scanner) and risk-limiting audits ( verify the scanner or hand counter)
- What’s the fix for the voting system? 1. Look at the election system as a very hackable security problem for the start. 2. Train your developers and engineers and teach them to hack and think like a hacker. 3. Hire hackers to get a different perspective on your problem and are security-minded.
Mihai Belu & Razvan Stere, @Electronic Arts
Presentation title: Security meets the world of gaming
- DevKits – hot stuff on the black market and are fully configurable.
- Anti-piracy – diminishing returns -> all games will be cracked if the offline play is possible, minimize player announce and performance hit, try to maximize time on the market
- Anti-cheating – ensuring a fair and fun field of play – > detection and prevention/modus operandi is just like malware for cheaters in gaming/incentive for cheating: competitive gaming prizes now reach or surpass professional sports levels.

Steve McGregory, Senior Director @Ixia
Presentation title: Implementing Continuous Offense, to Measure and Monitor Cybersecurity Defenses
- the solution to cybersecurity is the automation of self-hacking and remediation
- Continuously improve the network with vulnerability assessment, breach and attack simulation, pentesting and red teams, pre-deploying security testing
- What tools do hackers use? MITRE, Kali Linux, Empire, Metasploit
- Breach realism – Simulate attacks across each phase of the cyber kill chain
- Continuous validation of the enterprise-wide security infrastructure
- Quantify the impact of the latest security breaches and perform a security assessment
- If you can’t measure it, you can’t improve it.
- Educate network and security stuff – educate your people, enhance situational awareness for operators,
- The most important thing today is your data, your information.

Jun Li, Senior Security Researcher @360 Security Technology
Presentation title: Secure them all—From Silicon to the Cloud
- Silicon/Chip security – attacks vectors: boards, nodes (all types of devices)
- Chip reverse-engineering methods: Decap ->: microprobe to connect inside the chip, FIB: Focused Ion Beam – Circuit editing, make the connection, cut the connection, RTL (Register-transfer level), Fault injection, side-channel analysis
- Passive keyless entry system relay attack – demo followed
- “All protocols are secure until it is broken”
- Steal cars via a cellular network
- Hardware security measures you should consider and implement = secure elements in ECUs, firmware encryption, and verification, mutual authentication among ECUs
- DO NOT trust anyone on the communication link, only rely on what you can absolutely control over to implement your security

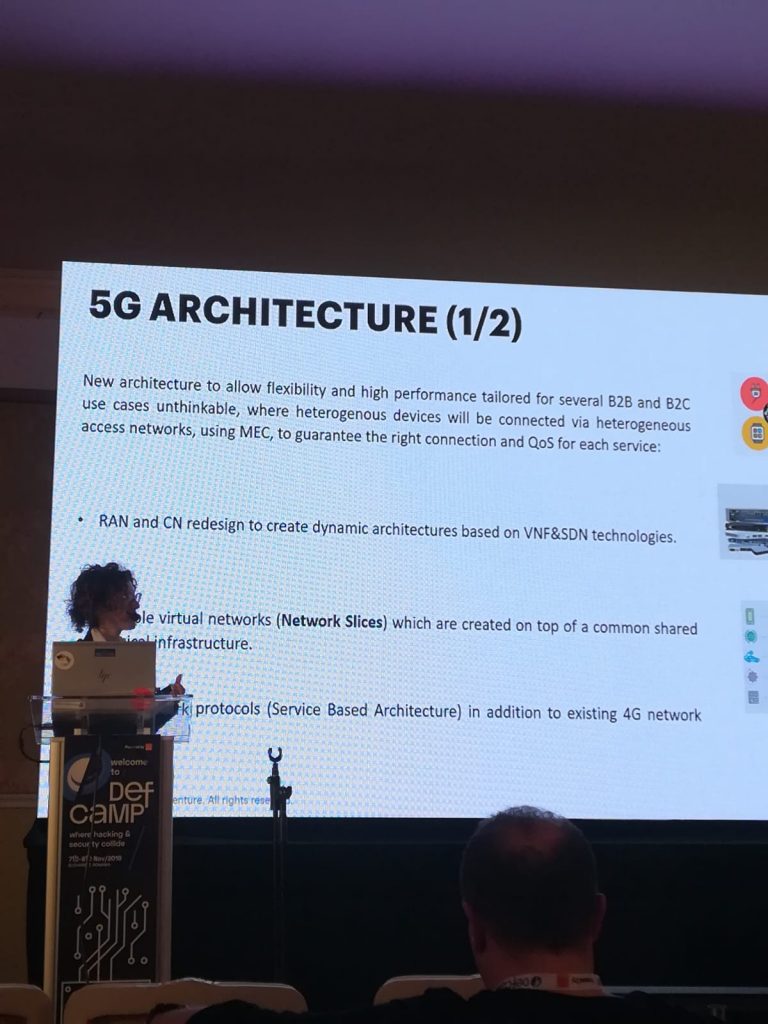
Rosalia D’Alessandro, Security Associate Manager @Accenture IT
Presentation title: 5G: Need for a comprehensive Cyber Security Framework
- 5G architecture allows more flexibility and high performance tailored for several B2B and B2C use cases
- 5G threats: heterogeneous devices, the security of front hauling and backhauling links, heterogeneous access networks, new signaling protocols based in HTTP, resource sharing-> Everything is shared and opened, and it could be a security issue, user privacy->user identity is bounded to devices, complex ecosystem, untrusted external network exposure, supply-chain integrity.
- 5G expands cyber risks, so there is a need to redefine the cyber strategy and try a new approach
Neil Roebert, Senior Information Security Consultant @F-Secure Consulting
Presentation title: Securing DevOps: Common misconceptions
- DevOps – complicated environment that works together
- DevOps refers to people – process – technology
- the code that is produced is your product and on the other side, you have the users
- the security-focused pipeline
- Attack scenarios encountered: secret management (Creates barriers between your devs and product) -> if an attacker can register on GutHub, you can get access to your data found on the account, then the Configured Infrastructure (CI) and access to sensitive information.
- Developer machines are getting easier to get access to due to most of them using unmanaged personal machines.
- Key takeaways: overcoming the mindset that DevOps is just an ideology, understanding the technology and assessing often overlooked systems from a holistic perspective, building resilient systems that can withstand attack.
