Steve has seen many changes in the infosec industry during his career of 30+ years. His knack and passion for educating people about cyber security has led him to speak to people of all backgrounds at tech events around the world. His latest mission consists of gathering actionable application and security intelligence that can better protect customers globally.
We talked to Steve about about a CEO’s worst fears when it comes to cyber security and many more topics.
He generously shared his insights, which we’re excited to share with you as a preview to his talk at DefCamp this year!
“The CEOs I speak with are beginning to have the awareness and fright that comes with every publicized breach. I often hear different forms of the same question:
Have we spent enough or too much on cybersecurity?
What’s the ROI on my cybersecurity spend?
Am I doing enough, not enough, or too much?
For most, the answer does not come easy. One thought is that the lack of a known breach would mean that I’ve spent enough or possibly too much. The other side is if you were hacked, does that mean you didn’t spend enough money or effort?
Also, some CEOs think that since they have an IPS or NGFW, they’re protected. It’s like in the PC world, where someone might say, “I use an Apple Mac, and since there’s no malware for Mac, I’m safe!”—and yes, I’ve heard both. It’s rather simple and mistaken, probably dangerous for that company, because we all know the cybersecurity chain is weak throughout an organization that thinks that way.
The least obvious thing is that cybersecurity is complex and this causes misguided notions or overthinking. We must apply a simple mental model with success metrics to cybersecurity.
Look at the measurable findings, not the unknowns, no cybersecurity defense is impenetrable.
Look at the problem as building a process to add resiliency into the system, how fast can you react to a cybersecurity event. Continuously measure and count the vulnerabilities found and fixed, and continuously assess your people, systems, and processes for their ability to act and recover.”
Digging deeper into the topic, we wanted to explore how C-level executives’ understanding of the cyber security field have changed over the past few years.
“Pinpointing wins is difficult because we mostly hear about the losses. These days, I see it from a unique position in that Ixia provides products to assess network resiliency and security control efficacy. Five years ago, I’d go speak to executives and security operations people about performing testing on their network and security controls.
The responses I got over and over was “Why should I test those products? I paid the vendor for the product and that product has already been tested!”
It’s dangerous to overlook the fact that those devices will probably not perform in a live network as they do in a best-case manufacturing test. Today, I hear much less of that response. I believe that awareness is and always will be an issue for cybersecurity industry; it’s true about most everything really. I’m not just talking about the advanced level of hackers these days or the dangers that exist, I’m also talking about the lack of awareness about the weaknesses in the products you deploy to protect your network.
I believe that I’m seeing wins in the form of executive’s awareness that there’s no single silver bullet in cybersecurity defenses.
Layered security is the best practice and validating each of the layers to help you shore up weaknesses in one layer with another layer.
A loss to me is when someone purchases a product purely based on the specification sheet provided by the vendor, and I still see this today.” In spite of this evolution, the perspective of business executives is still riddled with misconceptions.
With Steve’s help, we tried to better define some of these.
“There are many misconceptions about cyber security. One is that you can train people and end-users to prevent cyber security issues. Wrong; you can’t train people to not be human, we all have our fallacies. Next, believing the marketing spiel of security companies. I’m most bothered by how companies tout their products as being strong in every way possible.
You can’t put together an architecture that fits everything that will come at you and still provide usability and network performance that’s expected by users these days. This is an area that I focus on here at Ixia, architecture of security products and their benefits and weaknesses when pressed in different ways. Business management relies heavily on spec sheets and trust in a product without validating it in their network; no single network is the same and no single device can handle all networks with the same level of protection.”
So where does the disconnect between infosec specialists and business people start? Steve has a few thoughts on this, based on his diverse and complex experience:
“Infosec people think that everyone should care or know about cybersecurity. While an awareness is needed, business people should not be required to be infosec experts.
Bankers must be great at banking, accountants must be great at counting, and cyber security specialists must be great at cyber security; we cannot expect business people to understand technology.
Technology is complex and cyber security of that technology is even more complex. Information security specialists must learn to promote technology to solve issues in cyber security, and the cyber security technology must be built into the methods of doing business.
Take the password dilemma, too many people reuse passwords and many information security people think they can teach business people patterns to creating unique passwords to solve the issue.
I think we should remove the human factor all together, use technology to solve the problem and let people focus on the business they are trained to perform.”
Besides these ingrained human habits, we went on to explore how decision-making in companies impacts security to either strengthen it or, more frequently, weaken it. “Historically, there’s been one major decision that usually lowers a security setup, and that’s when packet delivery becomes more important than packet security. It’s okay to make that decision if you have a properly deployed layered security model.
The world of intrusion prevention requires that every packet is inspected and a decision made to block or let that packet go, there’s not always enough time to fully understand if the packet is malicious. This is due to the business needs to continuously deliver packets and keep business rolling. To balance these needs, it is best to have another network layer meant to inspect and perform analysis on all traffic without any concern of network performance. This layer will consist of visibility tools or detection systems.
Not applying a defensive, in-depth security solution is lowering your security setup and increasing risk.
Another strategy to balancing network performance and security is, don’t try to blanket everything with the same level of security controls. Knowing the most valuable assets and where your valuable data resides is important. At a minimum, it will highlight an area where you should spend more or apply more security controls.” But poor security patterns are not rooted in the business departments alone.
Steve prompts infosec specialists to look at their own behavior and making a change before prompting others to do so.
“Many of the poor security patterns I see are caused by the security industry in the first place; mainly because the industry is trying to make money. The drive to make money will push people into touting their solutions in ways that cause a lot uncertainty or doubt in other products.
I don’t think the industry itself is tackling this problem, but I do see the approach of “sharing is caring” can make a positive difference. Not just sharing Indicators of Compromise, but sharing truths about the strengths and weaknesses of the many different products available today. No one product does it all, and unless you know the weaknesses of a product, you cannot apply proper countermeasures to mitigate situations that will arise.”
So how does one reconcile the longstanding struggle to balance security objectives and business targets?
Steve believes it all starts with thinking of them together instead of prioritizing one against the other: “Start with planning them together, from the beginning. Of course, if you have already implemented a business with no security objectives implemented then you are in for quite a ride. Unfortunately, this is the ride most companies are on.
Change is hard for many people to handle, and it is easier for them to do something a way they’ve always done it. This is problematic and a very difficult hurdle to get over. In this case, it will only occur if it comes from the top down; meaning executives must place the goals in front of the teams and provide the support to implement security into the business operations while still hitting business targets.”
Moving on to the next step and possible action, we wanted to ask what Steve believes about helping business integrate security as part of their mindset.
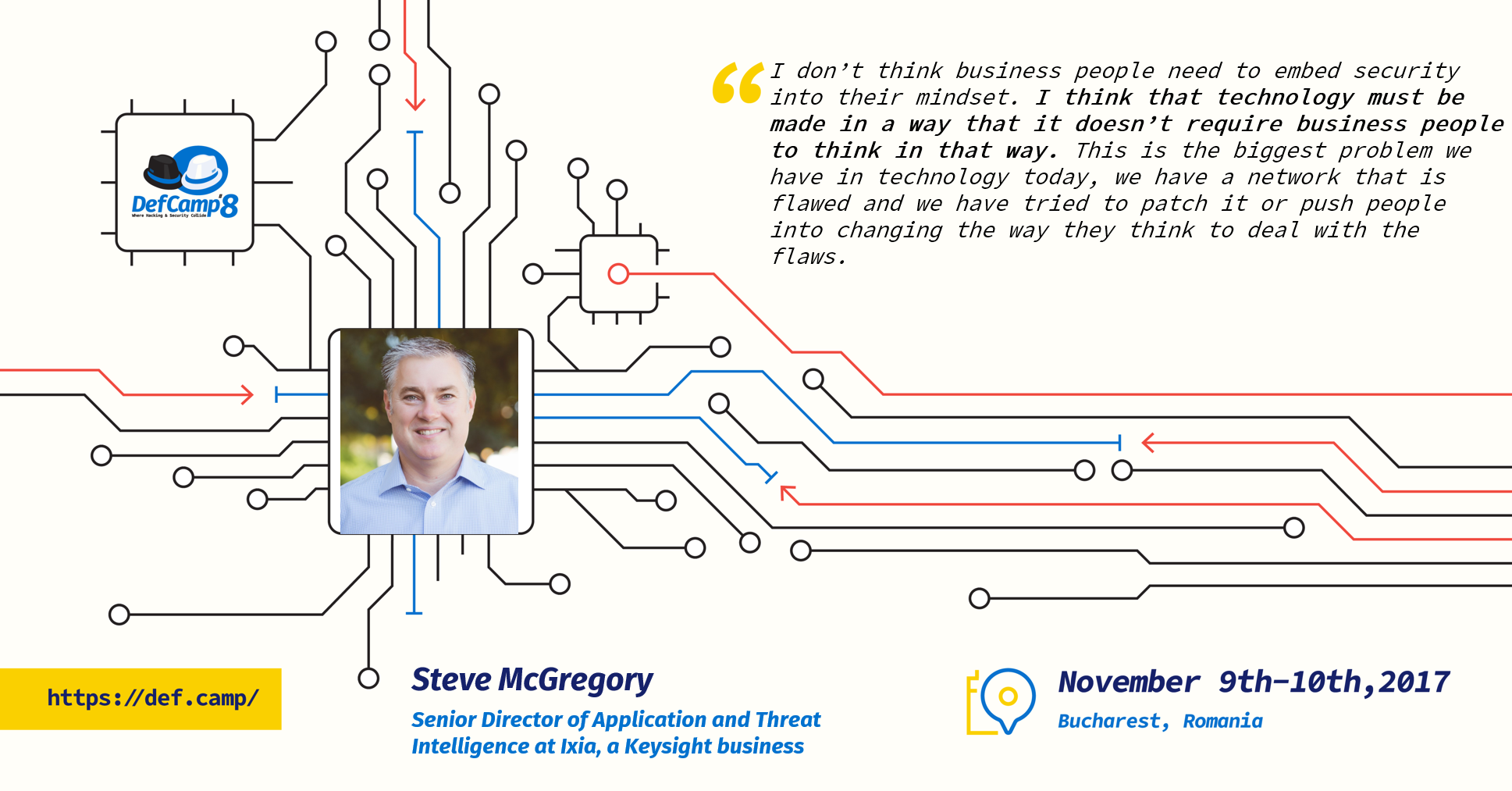
“I don’t think business people need to embed security into their mindset. I think that technology must be made in a way that it doesn’t require business people to think in that way. This is the biggest problem we have in technology today, we have a network that is flawed and we have tried to patch it or push people into changing the way they think to deal with the flaws.
We must change technology, we must fix parts of the Internet that are flawed, and we must build security into the technology from the beginning so that people don’t need to embed it into their mindset. Another misconception is when people say that we have a shortage in skilled talent in cyber security industry today. Rather, I think we have a shortage in companies that are willing to invest in people to build a skilled workforce. So, yes, we have a shortage, but the shortage will remain until companies take cyber security serious enough that they will invest in their people to enhance skills.”
Right before you go, you have to read what Steve plans to do at DefCamp this year, because we believe that many of us resonate with this mission:
“I’m at a stage in my career where I spend most of my time looking around the corner, examining what we will look like when we get there without change—then applying changes to help us much better handle the future problems. If I can reach a few, and cause them to think differently or approach matters in new ways, then I’ll have achieved my goal.
DefCamp attendees are the people who will solve many of the problems we have today, and if I can help energize them, if I can cause them to think outside the box, then I hope that will make the Internet a safer place for all. Ultimately, when I started my career it was the vision of what the Internet could be for humanity that started me on this trip and I wish to make my dent in the universe by helping make the Internet a safe place to share information and learn about things you may never have otherwise had the chance.”
You can meet Steve and other amazing members from Ixia, a Keysight business between 9-10 November, at Crystal Palace Ballrooms, Bucharest, during DefCamp – the largest hacking and cyber security conference in CEE.
DefCamp 2017 is powered by Orange România and it’s organized by the Cyber Security Research Center from Romania (CCSIR) with the support of Ixia, a Keysight Business as Platinum Partner, and with the help of Bitdefender, SecureWorks, Amazon, Enevo Group and Bit Sentinel.
The interview & editing was made by Andra Zaharia.