It’s often the things you don’t see or know that cause the biggest anxiety when you’re trying to figure out your way through the infosec industry.
We believe it’s our responsibility to bring as many of those things into the light – things like thought processes, nuance in dealing with internal challenges, and what motivates cybersecurity pros to do their best day after day, no matter how difficult it gets.
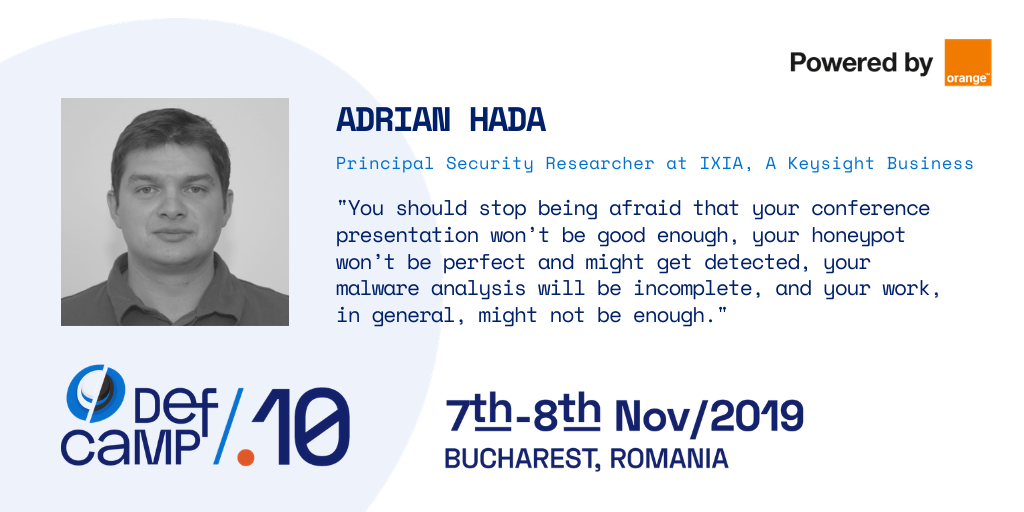
This interview with Adrian Hada, Principal Security Researcher at IXIA, A Keysight Business, provided the perfect opportunity to do so! That’s because Adrian is candid about the true challenges in this profession and he’s also actively contributing to finding solutions along with his colleagues.
The insights he shares in this interview are bound to spark your curiosity or trigger some sort of reflection or inspiration. You may gain a new outlook on things you deal with every day.
Whatever you take from it, make sure to share it with others. Maybe even at DefCamp or during lunch with your team. It takes all of us to do this right.
We should talk about this more frequently in the industry
It’s clear Adrian has experienced this first-hand in many contexts because he truly understands the power of…
“Cooperation.
We have all seen and heard of breaches being caused by security regulations being ignored, management decisions leading to reduced investment in security, and other issues that could have been solved by simple interaction that is not bogged down by politics or misunderstandings.
All defenders are in the same boat and it is the same boat that users and organizations are in. We all share the common goal and desire to feel safe and protected but sometimes fail to do that because of less than perfect cooperation attempts.
Some things have improved over the years – think of the NSA and GCHQ open-sourcing tools and actively participating in security conferences – but there still is a lot of work to do in this respect – cooperation inside the InfoSec industry, between the industry and governments, between the industry and end-users, and even inside each organization.”
To reach this level of cooperation Adrian describes, we believe we – the entire community – need to use empathy a lot more frequently and try to avoid our inherent cognitive biases. It may not seem so for industry outsiders but these are two of the most important types of work in cybersecurity.
Cultivating a growth mindset also helps infosec pros identify the bigger issues in the cybersecurity process. They very often have to do with people and Adrian touched on a very important element that affects almost all the rest.
“Our main adversary right now is the issue of false positives in detection and blocking decisions.
Alert fatigue is real and security operations centers can easily become flooded by false positives. Too many alarms in a code scan, penetration report or event monitoring system will also lead to a sense of either helplessness or indifference inside development and operations teams.
Human beings need to be able to focus and we try to do something that only raises real, threatening alarms instead of simply creating more panic and fatigue.”
Helping others is one of the strongest motivations we’ve observed in people who work in cybersecurity and thrive at it. Whether it’s securing critical infrastructure or helping other specialists have a bigger impact on where it matters, this type of contribution makes work meaningful and rewarding.
Adrian also talks about this last bit and how it ties into his own experience:
“As I mentioned before, we are heavily focused on not creating any false positives and raising needless alarms.
We’ve had one customer credit a product by reducing 80% of the manual investigation work that needed doing on a daily basis. That’s more time for the defense teams to investigate alerts and truly identify risks as well as less of a burden on the people doing this work.
Having worked in a similar position at some point, I feel like I’m helping create safer organizations and happier and more relaxed security specialists.”
That’s a pretty great mission to have, isn’t it?
The great part is that you can become part of this process too if you aren’t already. It’s a matter of doing the work and discovering where your skills and know-how make the biggest difference.
These wise words from Adrian work wonders if you want to stop hiding behind the excuses our brain makes sometimes when things get difficult.
Trust yourself and do the work you love
“You’re not perfect, don’t have perfect knowledge and can’t do perfect things. That makes you human, just like any other InfoSec person, experienced or not.
You should stop being afraid that your conference presentation won’t be good enough, your honeypot won’t be perfect and might get detected, your malware analysis will be incomplete and your work, in general, might not be enough.
The truth is some of the lowest quality work I’ve done brought in some of the highest quality content for my research. When in doubt, unless it’s something that is truly life-threatening, risk failure. Everyone does that.
So, start working on your honeypots, analyze that malware today, and submit the cool work you do as presentations for Defcamp 2020.”
We don’t know about you but reading these supportive thoughts really got us in a “let’s do this!” mood. Plus, it got us even more stoked for all the presentations we’re about to see on stage at DefCamp! We’re SO ready to soak in all those insights!
Speaking of presentations, you may know IXIA always brings great research each time they attend DefCamp. Because we were curious to find out how they make that happen while so many things compete for their time and attention.
Here’s what Adrian shared with us:
“We try to dedicate as much time as possible to research and would definitely love to see 100% of our time going in that direction. The truth is that’s not always possible – sometimes you must spend your time explaining to your hosting provider that your honeypot is a trap for attackers and not something that is legitimately vulnerable and will take down their network.
Other times you spend weeks trying to debug that sandbox code that suddenly stopped working. But security is an adversarial and ever-changing domain, so research is vital. We always try to stay on top of new tools, techniques, and procedures and make it hard for attackers to evade our detection systems.
It’s a continuous effort, it’s time-consuming and it can be completely frustrating at times, but this is how we build a safer online environment for everyone.”
Plus, we’d say research has brought many interesting topics that generalist media outlets covered, research that finally broke outside the boundaries of the field.
This made cybersecurity issues more visible, thus making CEOs more receptive to needs and proposals from their infosec teams.
That’s what makes Adrian’s observation on the best advancement in cybersecurity from the last few years so interesting!
Cybersecurity awareness is our biggest win
“It might sound strange, but I won’t name anything technical. Instead, I would say awareness is our biggest win. And, to make things even stranger, we must “thank” the authors of several resounding breaches for that.
There is more and more awareness around the fact that we need to build safe systems and keep them operating safely. Cybersecurity specialists are being sought out in numbers, more and more useful tools appear, and the public is becoming less reluctant to accepting smaller or greater inconveniences for the sake of security.
Multi-factor authentication, for example, would have seemed like a time-waster several years ago, yet more and more people are accepting that inconvenience now for the sake of security.
We’re still far away from being perfect but a lot has changed – I’ve even seen non-technical people who are now able to recognize tell-tale signs of a phishing email and that is something we need more of.”
Cheers to that, Adrian!
We’re really honored to have speakers like Adrian Hada on stage at DefCamp, giving their best to the audience, both in terms of knowledge and career-building advice.
But don’t leave just yet because Adrian has a call to action for you, as well as other infosec specialists and enthusiasts.
“I’d encourage them to see as much of what’s going on in the InfoSec world as possible.
DefCamp might give you insight into how to perform better at your job. You might meet your next great friend or co-worker or come up with a new and brilliant research idea. It might help you realize that you can add value to the world by sharing your expertise with it.
Worst-case scenario, you just walk around for two days gathering SWAG. But I’m sure that if you try to see a couple of presentations you find interesting, maybe one or two that seem too difficult for you, try some of the Hacking Village challenges and simply enter a conversation with some of the many attendees, you’ll gain much more.”
We hope to meet you at DefCamp on November 7-8!
Until then, check in with us once in a while. Infosec wisdom nuggets often pop up here, on the blog.
This year, we’re taking DefCamp to the next level with the help of our main, long-time partner, Orange. With support from IXIA – a Keysight Business, Secureworks, UiPath, Bit Sentinel, Thales, and other selected tech companies that value the power of community, we’re building valuable, hands-on learning experiences for 2000+ attendees from all over the world!