Walter makes a very persuasive point when he talks about security, be it online or IRL. He brings together notions from physical safety and cyber security which makes the listener’s (or reader’s) mind click on that “a-ha!” moment.
In preparation for his talk at DefCamp, we sought to explore Walter’s perspective on security and the vulnerabilities that plague us, be they technical or specific to human nature. A core topic that’s on everyone’s mind in the infosec industry is how software complexity is increasing the number of vulnerabilities.
As a result, we decided to kickstart the discussion with just that. “It is true that more (and bigger) software has more problems. Having a world with less software is not an option. The software is actually doing stuff that is helping us. So this should not be an excuse for deploying vulnerable software, but an incentive to make software better. I believe that security is just one aspect of overall software quality. We need to educate software writers to make quality software, but it’s maybe even more important to educate people to buy quality software, or ask for quality software to be build.”
In cases where the market keeps people from making or buying low quality software, governments should step in. The biggest problem in all of this is that it is very hard to define what quality software is. Yes, there are metrics that you can use, but they only tell you so much.”
Ultimately, the government is responsible for quality and safety of critical infrastructure
Taking it a step further, we turned our attention to critical infrastructure and the software and hardware that helps it run. Who should be responsible for their quality and safety? Walter believes that “Ultimately, the government.”
But how can it be as secure as possible? How can this be defined?
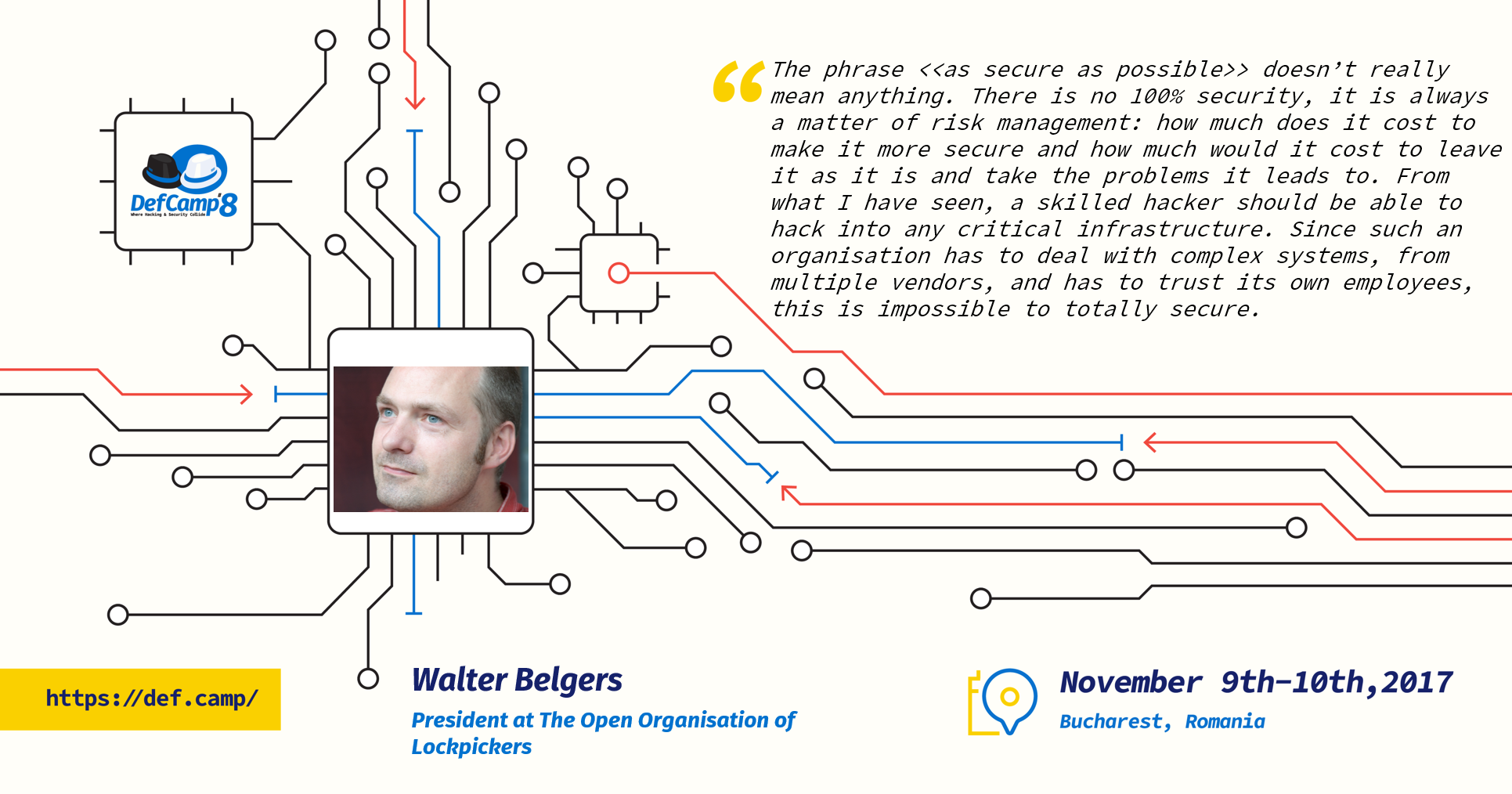
“The phrase “as secure as possible” doesn’t really mean anything. There is no 100% security, it is always a matter of risk management: how much does it cost to make it more secure and how much would it cost to leave it as it is and take the problems it leads to. From what I have seen, a skilled hacker should be able to hack into any critical infrastructure. Since such an organisation has to deal with complex systems, from multiple vendors, and has to trust its own employees, this is impossible to totally secure.” But certainly there must also be examples of best practice, teams and companies who got it right by making an effort in making their software platforms safer.
“For example, there was an insurance company whose in-house built web site was hacked. We tested the web site and it was full of vulnerabilities. We gave a secure programming training for the developers, using examples from their own code. Every subsequent web site that we investigated that they had built, was more secure. This was in a matter of months. For them, it was great to see and getting acknowledged that the quality of their software improved.”
Infosec specialists speak the same language, but when it comes to home users, the perception is very different. For example, do they react differently to a hardware vulnerability versus a software one?
“A hardware bug in a car could be that in certain circumstances, the airbag would not work. A software bug in a card could cause the exact same thing. Fixing it works the same (a recall of the car). For the home user, there is no difference. It’s a problem (or a hassle) in both cases.”
Users only care if they are directly affected.
What about IoT products? What makes them so fascinating to users that most don’t even consider the associated security risks? “Users do not consider risks of the products they use, whether it be IoT or something else. Users only care if they are directly affected. If their home computer is part of a botnet, they won’t care if they don’t notice. Only when something happens, it’s a problem. Hence, home users do not really ask for quality (safe) products. This is the same with IoT.”
Going back to a point previously made, the infosec industry knows that 100% security is unattainable. But what do the millions of home users think about this? Do they realize it? Here’s what Walter had to say on the topic: “The home user is not very interested in security as long as “it works”. From an end-user perspective, it is all about functionality (does it do what it should do) and security (does it not do what it should not do) is not very important (until something actually goes wrong). So they are not telling themselves lies, security is just not on their list of properties a device should have, as it does not add any “useful” functionality. What changes their mind is an incident, but then it is too late. I think the only solution is to ban insecure devices from the market, if not, they will continue to be bought en masse.”
The only thing that will help is continuous education.
So, can anything change the “it can’t happen to me” argument that most people use when confronted with the idea or proactive online safety? “The only thing that will help is continuous education. When nothing bad happens, people are becoming more and more relaxed about security. This is inevitable.”
Is there anything to learn from the attackers so we can be better prepared for their attempts to compromise our safety? “Nothing much. We want to defend and they can only teach us how to better attack. But of course, we need to keep on investigating their modus operandi to be able to react to attacks in an effective and timely manner.”
We also wanted to find out about what Walter believes is the next big challenge in cyber security and how he envisions tackling it.
“For almost any company I’ve been at, I think the most difficult and important challenges are:
– patching ALL systems continuously (also the legacy and test systems)
– segregate as much as possible within the organisation
– educating all users about social engineering attacks.
On a global scale, I see that we now have a lot of monocultures, like iOS, Nginx, BIND, Postfix, etc. Because of this, attacks (0 days) on these systems will have a huge effect. It would be best to get a bit of diversity.”
After reading this interview, you may want to know that Walter is set on sharing “that security in physical systems is, in the end, not so much different than in IT” at DefCamp this year. We can’t say more, but you’re going to enjoy his talk!
DefCamp 2017 is powered by Orange România and it’s organized by the Cyber Security Research Center from Romania (CCSIR) with the support of Ixia, a Keysight Business as Platinum Partner, and with the help of Bitdefender, SecureWorks, Amazon, Enevo Group and Bit Sentinel.
The interview & editing was made by Andra Zaharia.